في حوادث برامج الفدية الأخيرة التي طالت مقدمي الخدمات الحكومية، ظل المهاجمون داخل الشبكات لعدة أشهر قبل اكتشافهم. وتجاوزت العواقب مجرد تعطيل أنظمة تكنولوجيا المعلومات، حيث أدت إلى انقطاع الخدمات، وإجراء تحقيقات رقابية، وكشف ملايين السجلات الحساسة. وفي بيئات القطاع العام واسعة النطاق، لا يمثل الافتقار إلى الرؤية مجرد تحدٍ تشغيلي فحسب، بل إنه يزيد من المخاطر على مستوى المؤسسة بأكملها.
تقارير تفتقر إلى المعلومات الاستخباراتية التشغيلية
لم يكن التحدي الذي واجهته الوكالة هو ما إذا كان من الممكن تفجير الملفات أم لا. بل كانت المشكلة الحقيقية هي ما يحدث بعد ذلك. فقد كانت بيئة الاختبار الحالية الخاصة بهم تُصدر تقارير، لكن تلك التقارير لم تكن توفر دائمًا العمق أو الوضوح اللازمين لاتخاذ قرارات واثقة، لا سيما عند التحقيق في التهديدات المحتملة من نوع «صفر يوم».
مع تزايد قدرة البرامج الضارة على التهرب وتعدد مراحلها، أصبح من الصعب تجاهل أوجه القصور هذه.
القيد الأول: عمق سلوكي محدود بالنسبة للبرامج الضارة المتطورة
فيما يتعلق بالتهديدات التي تستغل الثغرات الأمنية التي لم يتم اكتشافها بعد، فإن الرؤية الجزئية تشكل مخاطرة تشغيلية.
واجهت عمليات الكشف القائمة على الأجهزة الافتراضية صعوبات في الكشف عن التهديدات المتطورة المصممة لاكتشاف البيئات الافتراضية، أو تأخير التنفيذ، أو انتظار تفاعلات محددة من المستخدم. ونتيجة لذلك، غالبًا ما كان المحللون يتلقون بيانات سلوكية غير كاملة.
وقد أدى ذلك إلى ظهور ثلاث ثغرات رئيسية:
- لم يتم اكتشاف السلوكيات الخفية، لا سيما الحمولات الموجودة في الذاكرة أو المُعدة مسبقًا
- أصبح إعادة التحليل اليدوي أمراً شائعاً، مما أدى إلى إطالة مدة التحقيق
- تراجعت الثقة في نتائج الفحص، لا سيما فيما يتعلق بالملفات المجهولة أو المشبوهة
القيد الثاني: التقارير التي تتطلب تفسيراً يدوياً
لم يكن الخطر الأكبر هو نقص البيانات، بل عدم الوضوح.
قدمت بيئة الاختبار نتائج مفصلة، لكنها لم تكن دائمًا معلومات استخباراتية قابلة للتطبيق. فقد كان على المحللين أن يستخرجوا المؤشرات يدويًّا، ويُفسروا مسار التنفيذ، ويربطوا النتائج بين الحالات المختلفة باستخدام أدوات خارجية.
وقد أدى ذلك إلى:
- استغراق التحقيق وقتًا أطول أثناء الحوادث الجارية
- عدم اتساق تبادل المعلومات بين فرق مركز العمليات الأمنية (SOC) وفرق الاستجابة للحوادث الإلكترونية (CERT)
- بيئة اختبار تعمل كأداة تحليل جنائي، وليست محركًا للكشف
القيد الثالث: المعلومات الاستخباراتية التي تعذر تفعيلها عملياً
المعلومات الاستخباراتية التي لا يمكن تفعيلها هي معلومات لا يمكنها الدفاع.
وحتى عند تحديد التهديدات، لم تكن النتائج تُثري أو تُنظم أو تُيسر مشاركتها بشكل منتظم. مما جعل من الصعب على الوكالة:
- تغذية سير عمل البحث عن التهديدات
- ربط العينات والحملات ذات الصلة
- دعم تبادل المعلومات الاستخباراتية بين الوكالات
في تلك المرحلة، توصلت الوكالة إلى استنتاج مهم: لم يعد من الممكن أن يظل "الصندوق الرملي" مجرد خطوة منفصلة تنتج تقارير. بل كان لا بد أن يتحول إلى نظام قادر على إصدار حكم واحد موثوق به لكل ملف، يمكن للمحللين الاستناد إليه في اتخاذ الإجراءات الفورية.
من التحليل إلى الدفاع العملياتي
لم تكن الوكالة بحاجة إلى بيئة اختبار إضافية. بل كانت بحاجة إلى حل قادر على مواكبة التهديدات الحديثة وتقديم نتائج يمكن للفرق الاستفادة منها فعليًا. وكان هدفها واضحًا: بناء قدرة موحدة للكشف عن هجمات «اليوم صفر» قادرة على التصدي للبرامج الضارة المراوغة، وتقديم مخرجات بمستوى المعلومات الاستخباراتية، والتوافق مع سير العمل الحكومي الحالي.
ومن أجل المضي قدماً، حددت الوكالة أربعة متطلبات ترتكز على مهمتها وتركز على الحد من المخاطر وتحسين عملية اتخاذ القرار.
1. تحليل سلوكي أعمق دون وجود نقاط عمياء في التهرب
كانت الوكالة بحاجة إلى تحليل ديناميكي قادر على كشف سلوك التنفيذ الكامل — بما في ذلك الحمولات التي تعمل في الذاكرة فقط، والمشغلات المؤجلة، والهجمات متعددة المراحل المصممة للتحايل على البيئات الافتراضية. ولم يعد الرؤية الجزئية مقبولة، لا سيما في الأنظمة المقيدة حيث يمكن أن يشكل أي سلوك لم يتم رصده خطرًا تشغيليًا جسيمًا.
2. قرار واحد موثوق به لكل ملف
كان المحللون بحاجة إلى الوضوح، لا إلى المزيد من البيانات الأولية. وكان على الحل الجديد أن يدمج النتائج السلوكية ومعلومات الاستخبارات المتعلقة بالتهديدات في تقييم واحد متسق وقابل للتنفيذ. وكان الهدف هو تقليل الاعتماد على التفسير اليدوي ومساعدة فرق مراكز العمليات الأمنية (SOC) على التحرك بسرعة أكبر في اللحظات الحاسمة التي تتطلب اتخاذ قرارات.
3. معلومات استخباراتية يمكن تفعيلها وتبادلها
لم يكن من الممكن أن يقتصر تحليل البرامج الضارة على مرحلة الكشف فحسب، بل كان لا بد أن ينتج معلومات استخباراتية قابلة لإعادة الاستخدام. فقد كانت الوكالة بحاجة إلى مخرجات منظمة ومُثريّة من شأنها دعم عملية تعقب التهديدات، وتعزيز التعاون بين الفرق المختلفة، والتوافق مع الأطر المعترف بها مثل MITRE ATT&CK. وكان من الضروري أن يتحول كل ملف مجهول إلى معلومات استخباراتية قابلة للاستخدام، لا أن يظل مجرد تقرير منعزل.
4. التكامل السلس مع البنية الأمنية الحالية
كما كانت الوكالة بحاجة إلى حل يعمل في ظروف واقعية: مخرجات قابلة للقراءة آليًّا، والتوافق مع البيئات الآمنة، والقدرة على التوسع عبر عمليات متعددة المناطق دون إنشاء أقسام منعزلة جديدة. وكان لا بد أن تصبح "الصندوق الرملي" جزءًا من مسار الكشف، لا خطوة تحقيق منفصلة.
وبعد تلبية تلك المتطلبات، مضت الوكالة قدماً في تطبيق حل مصمم ليس فقط لتحليل البرامج الضارة، بل لدعم الدفاع التشغيلي على نطاق واسع.
ما الذي تغير على الصعيد التشغيلي
شهدت الوكالة تحسناً فورياً بمجرد انتقالها من نهج "التفجير" المعزول القائم على الأجهزة الافتراضية (VM) إلى مسار تحليل موحد يعتمد على المعلومات الاستخباراتية. ومن خلال تطبيق MetaDefender اكتسبت الوكالة رؤية أعمق للسلوكيات، وقرارات أكثر دقة، ومعلومات استخباراتية منظمة يمكن تفعيلها على مستوى جميع الفرق.
وبدلاً من إصدار تقارير ثابتة تتطلب تفسيراً، قدم النهج الجديد تقييماً واضحاً وموحداً لكل ملف، مدعوماً بأدلة سلوكية وتقييم لمستوى التهديد.
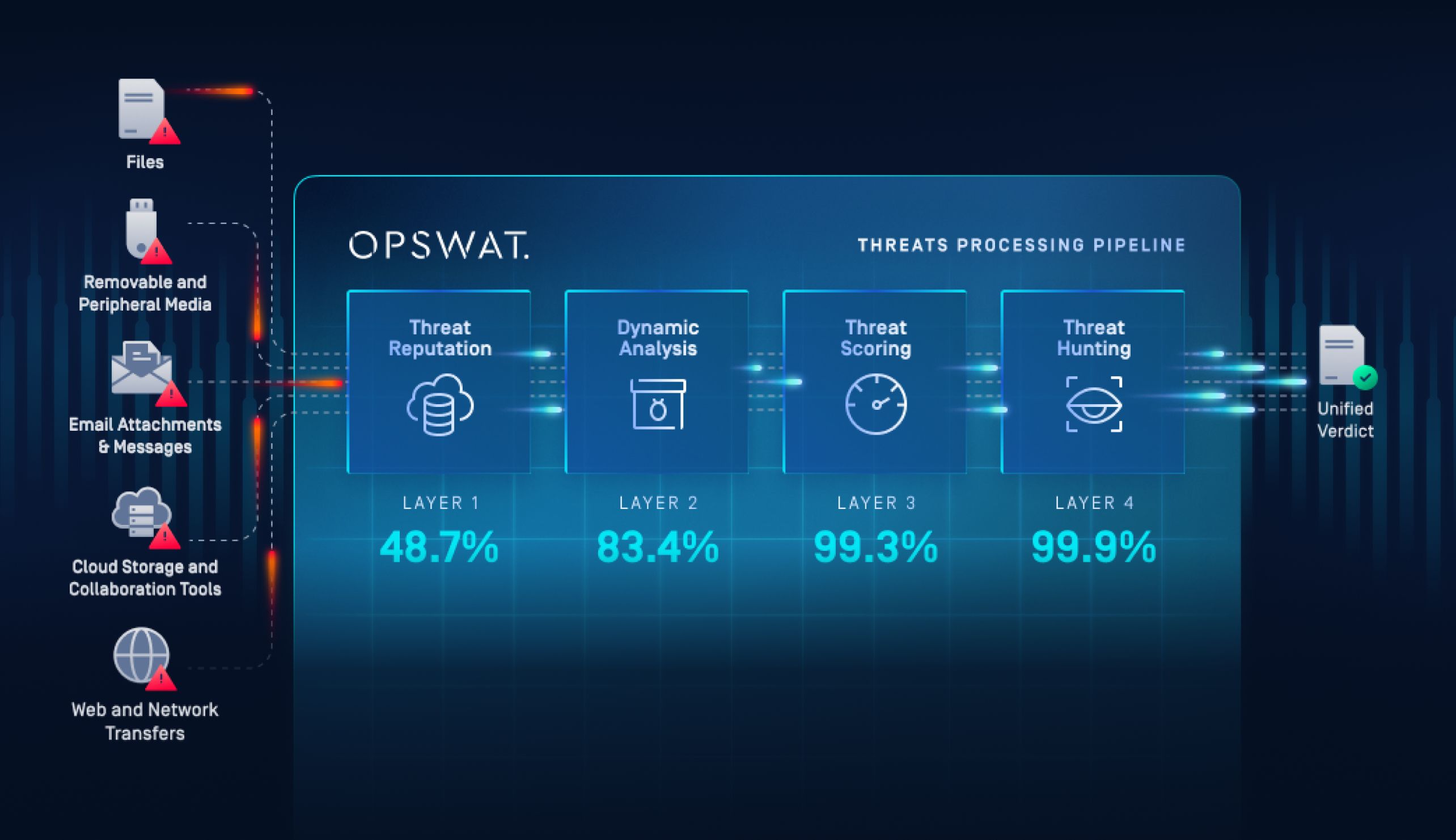
وكانت النتيجة عبارة عن مسار كشف مكون من أربع مراحل أجاب على أربعة أسئلة أساسية لكل ملف:
- هل هي معروفة وموثوقة؟
- هل يظهر سلوكًا ضارًا أثناء التنفيذ؟
- ما مدى خطورة ذلك استنادًا إلى الأدلة المتوفرة؟
- هل له صلة بحملات أو متغيرات معروفة؟
كيف تم تنفيذ ذلك
تم دمج MetaDefender مباشرةً في سير عمل الوكالة المتعلق بتحليل البرامج الضارة والاستجابة للحوادث.
تمت معالجة الملفات المشبوهة تلقائيًا من خلال:
- تحليل البنية العميقة لفحص سريع لأكثر من 50 نوعًا من الملفات
- التحليل الديناميكي القائم على المحاكاة لكشف سلوك التنفيذ الفعلي
- الاستخراج الآلي لمؤشرات التهديد (IOC) وتقييم درجة خطورة التهديدات
- البحث عن أوجه التشابه باستخدام تقنية التعلم الآلي لربط التهديدات ذات الصلة
تم تسليم النتائج بتنسيقات منظمة وقابلة للقراءة آليًّا. وقد أتاح ذلك إدراج النتائج مباشرةً في عمليات مركز العمليات الأمنية (SOC) وعمليات تبادل المعلومات الاستخباراتية الحالية دون الحاجة إلى تحويلها يدويًّا. وتطورت بيئة الاختبار (Sandboxing) من أداة تحليل جنائي قائمة بذاتها إلى محرك تشغيلي للكشف الفوري عن الهجمات، مدمج ضمن البنية الأوسع للأمن السيبراني بالوكالة.
الوضوح والسرعة وجودة المعلومات الاستخباراتية
انتقلت الوكالة من الاستفادة الجزئية من الرؤى السلوكية إلى الكشف عن الثغرات الأمنية في يومها الأول بمستوى استخباراتي. وأصبح تحليل البرامج الضارة أسرع وأكثر اتساقًا وأسهل في التوسع عبر الفرق المختلفة. وكان التأثير واضحًا في جميع المجالات: عمق الكشف، وكفاءة المحللين، والقيمة الاستخباراتية.
1. رؤية أعمق للتهديدات المراوغة والمجهولة
بفضل المحاكاة على مستوى التعليمات، كشف MetaDefender عن سلوكيات لم تكن قد تم رصدها من قبل. وأصبح من الممكن الآن تحليل سلاسل التنفيذ متعددة المراحل، والحمولات المؤجلة، والبرامج الضارة التي تراعي البيئة المحيطة، بمستوى أعلى من الاتساق.
ونتيجة لذلك:
- تحسن تغطية السلوك بالنسبة للعينات المراوغة
- ازدادت الثقة في الأحكام الصادرة بشأن الملفات المجهولة
- تطلب عدد أقل من العينات إعادة تحليل يدوي
2. تسريع التحقيقات وتقليل الجهد اليدوي
ساعدت النتائج المنظمة ونظام التقييم الآلي للتهديدات المحللين على العمل بسرعة أكبر وتقليل الوقت الذي يقضونه في تجميع الأدلة يدويًّا.
وشملت التحسينات التشغيلية ما يلي:
- دورات تحقيق أقصر
- تقليل عبء العمل على المحللين أثناء الحوادث التي تتسم بضغوط شديدة
- تبادل أكثر اتساقًا للمعرفة بين فرق مركز العمليات الأمنية (SOC) وفرق الاستجابة للحوادث الإلكترونية (CERT)
3. Threat Intelligence ذات جودة أعلى وقابلة للمشاركة
ساعدت المعلومات الاستخباراتية المدمجة حول التهديدات والبحث عن أوجه التشابه المدعوم بالتعلم الآلي في تحويل عينات البرامج الضارة المنفصلة إلى معلومات استخباراتية مترابطة. وأصبح بإمكان المحللين تحديد المتغيرات ذات الصلة والبنية التحتية المشتركة والحملات الأوسع نطاقاً بسرعة مباشرةً من نتائج التحليل.
وقد أتاح ذلك:
- تتبع التهديدات بشكل أكثر فعالية
- تحسين تبادل المعلومات الاستخباراتية بين الوكالات
- تحليل بأثر رجعي على عينات سابقة
من أداة التحليل الجنائي إلى محرك الكشف التشغيلي
قبل التنفيذ، كانت تقنية "الصندوق الرملي" تُستخدم كإجراء استباقي للتحليل الجنائي. وبعد نشر نظام MetaDefender أصبحت هذه التقنية جزءًا أساسيًا من مسار الكشف عن الثغرات الأمنية في يومها الأول لدى الوكالة، مما ساهم في اتخاذ قرارات أسرع، وزيادة الثقة، وتوفير دفاع أكثر قابلية للتوسع.
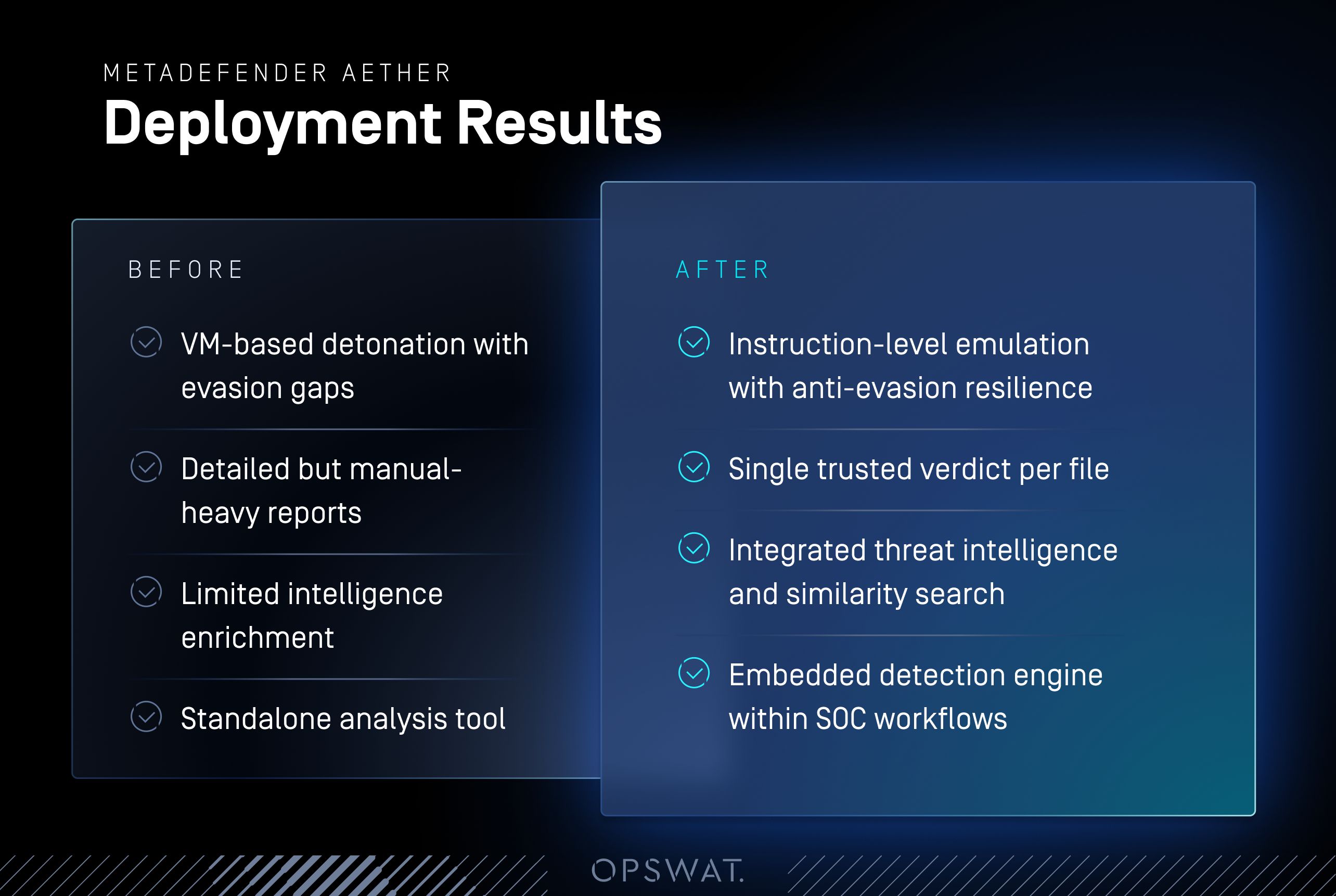
الكشف عن الثغرات الأمنية في يومها الأول في مجال الدفاع الحكومي
كان التحدي الذي واجهته الوكالة واضحًا: فقد كانت أنظمة الحماية المعزولة القديمة توفر تقارير، لكنها لم توفر الوضوح التشغيلي. وأدت البرامج الضارة المراوغة، والتفسير اليدوي، ومحدودية تعزيز المعلومات الاستخباراتية إلى خلق مخاطر في أنظمة تتطلب اليقين بشكل حاسم.
من خلال تطبيق MetaDefender قامت الوكالة بتحديث نهجها في تحليل البرامج الضارة. فقد كشفت المحاكاة على مستوى التعليمات عن السلوكيات الخفية. كما أثرت المعلومات الاستخباراتية المدمجة حول التهديدات وعمليات البحث عن أوجه التشابه المدعومة بالتعلم الآلي كل عملية تحليل. واستبدل تقييم واحد موثوق به التقارير المتفرقة.
وكانت النتيجة قابلة للقياس:
- رؤية أعمق للتهديدات المراوغة والمجهولة
- تحقيقات أسرع وأكثر اتساقًا
- مخرجات استخباراتية مناسبة للمشاركة على نطاق حكومي
- ثقة أكبر في حماية البيئات المحمية
بعبارة أبسط:
- التحدي → عمق محدود لبيئة الاختبار ووجود عقبات تشغيلية
- الحل → كشف موحد لـ«ثغرات اليوم صفر» قائم على المحاكاة ومزود بقدرات استخباراتية مدمجة
- النتيجة → استنتاجات على مستوى الاستخبارات تعزز الدفاع السيبراني الوطني
لا تكتفي الوكالات الحكومية بسجلات التفجيرات فحسب. بل تحتاج إلى الوضوح والثقة والمعلومات الاستخباراتية التي يمكنها الاستفادة منها على الفور.
تحدث إلى أحد خبرائنا لتتعرف على كيفية قيام MetaDefender بتحديث نظام الكشف عن هجمات "اليوم صفر" لدى شركتك.